Security for Your Microsoft 365 Login

Your Microsoft 365 account is a prime target for cyber criminals. They want you to give them your username and password so they can get into your account, sneak around, and discover how they can monetize their infiltration of your organization. Having Multi-factor Authentication (MFA) has put up a big barrier to cyber criminal sights on Microsoft accounts, but it’s still happening. Being aware of how they’re doing this will help you to avoid becoming a victim.
It usually starts with a phishing email that entices the recipient to click on a link that takes them to a fake Microsoft login page. Once account credentials are entered, there may be no sign that a compromise occurred, and the victim thinks nothing of what just happened. Meanwhile, the hacker begins to snoop around the account holder’s messages, gathering information that will be used to plan and execute their big hit.
Let’s look closer at this popular cyber criminal tactic so that you can avoid becoming a victim.
How Cyber Criminals Get Access to Your Microsoft 365 Account
First, it is important to understand what the malicious actors are after – which in most cases is your username and password. As mentioned, the credentials you use to sign-in to email, Teams, your computer, or another website are valuable to hackers and bad-actors looking to slowly siphon information and details from your everyday communications.
Second, with the large majority of email and file sharing now taking place on cloud services like Microsoft 365 OneDrive or Facebook, phishing emails will often imitate the ‘look & feel’ of these servers. Font, colors, and logos are all very easy to replicate and many of these phishing attacks have authentic looking websites setup to look just like your everyday Microsoft 365 login.
Knowing what the malicious actors are after and how they disguise their tools is the first step of defense. The next step is awareness – not just a general overview – but rather a distinguished set of ‘features’ or ‘unique cues’ that force a user to take notice.
How to Spot a Fake Microsoft Email and Login Page
The XPERTECHS Security Operations Center recommends the use of specific corporate branding, colors, fonts, and customized messages to help users distinguish between a fake and “the real thing”.
Below are some examples of a phishing message and how to spot a fake:
Example 1: Email Received from “Microsoft”
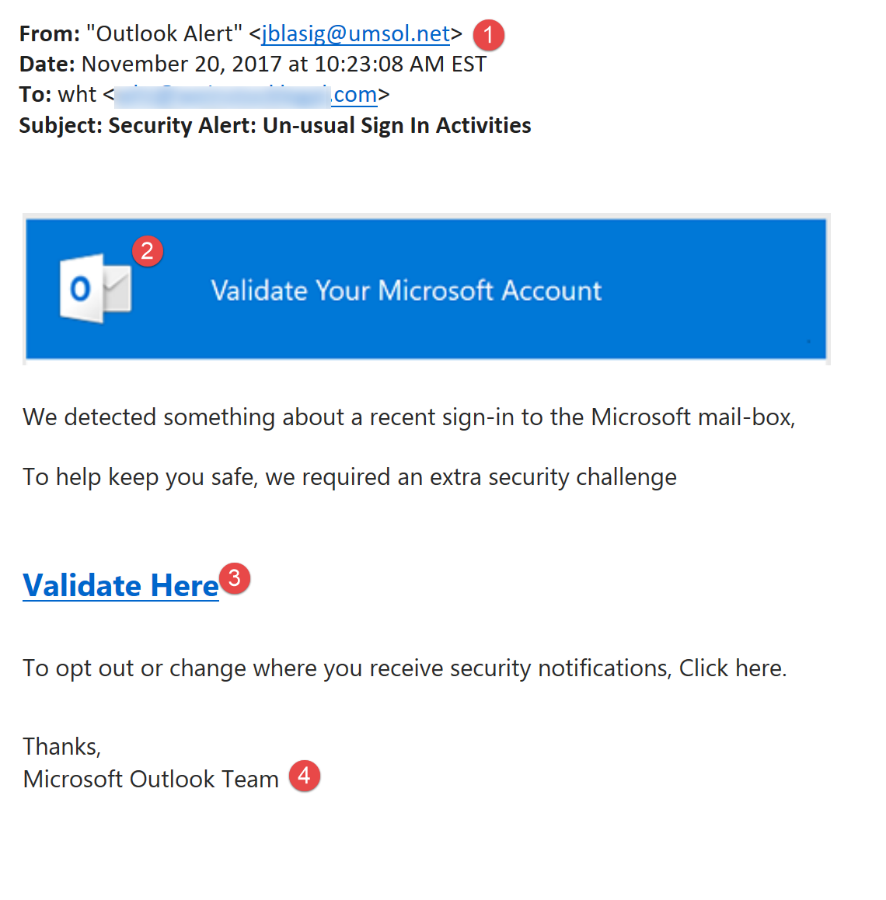
- Messages will often come from a legitimate address (this is usually an account that was compromised)
- Fake Logo or font will be used to make the message appear legitimate.
- A link or prompt for action (see next screenshot for detail)
- A false greeting or text to make the message look official
Example 2: Fake Office365 Login Screen
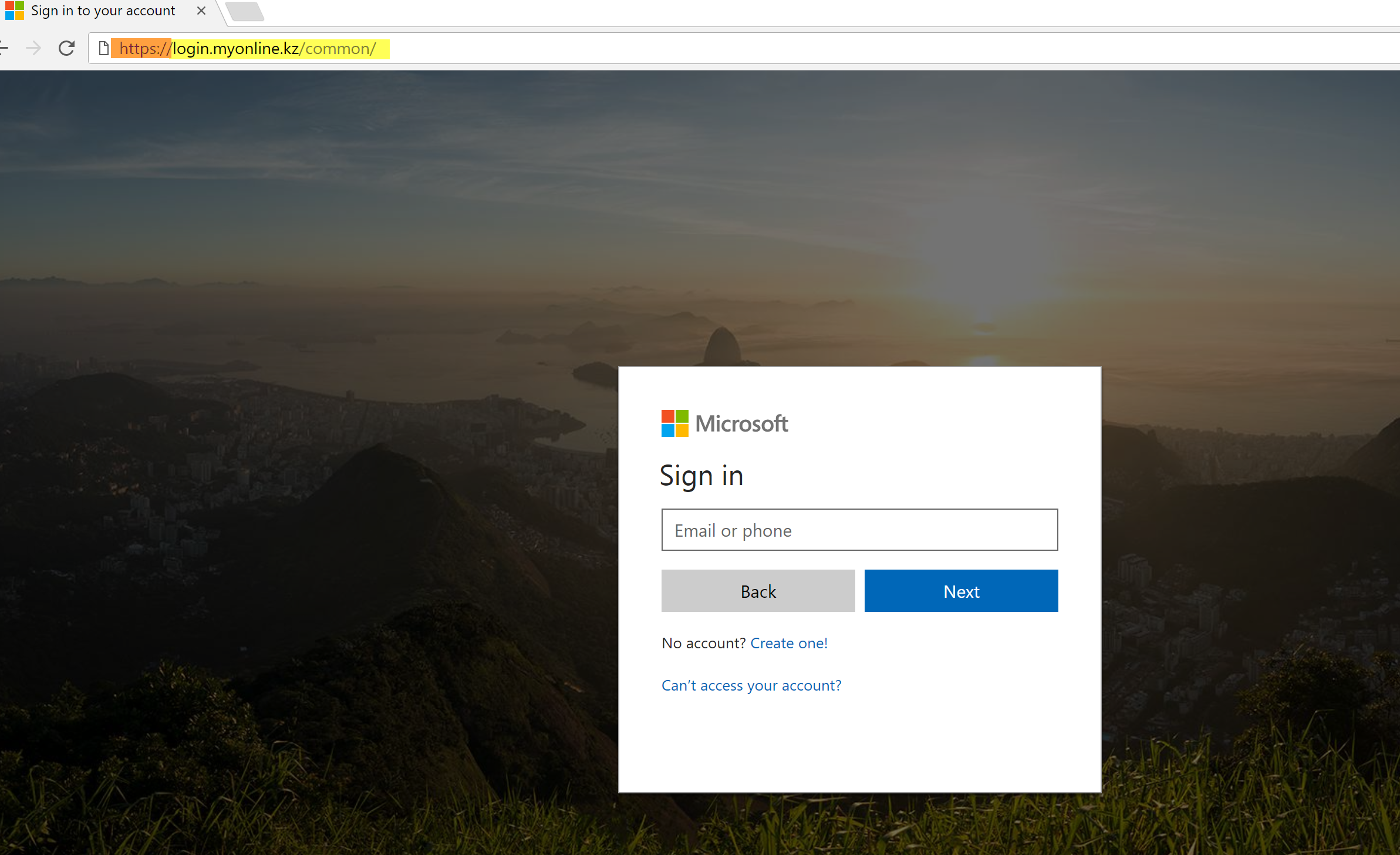
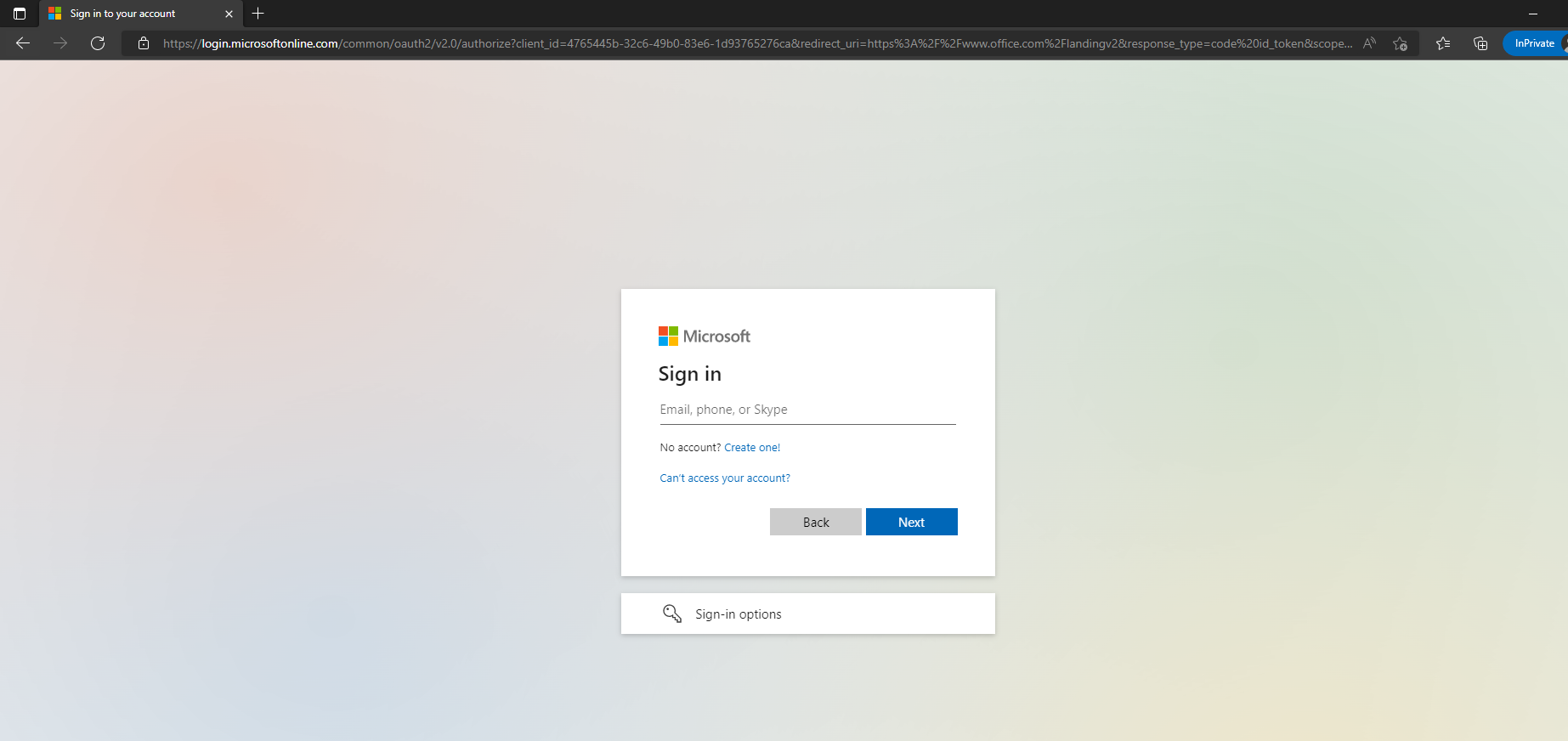
Aimed at convincing the user to enter their credentials, phishing emails are increasingly leading users to fake login websites that capture keystrokes of the user. Below is an example of a fake Microsoft 365 Login Screen.
- Legitimate sites have a URL that will always end with their company domain + “.com” Ignore anything before the “Microsoft.com”
- Most all legitimate sites have “HTTPS” – however it is possible for a fake site to have HTTPS. Be cautious and always look at the full URL.
Example 3: Legitimate Office 365 Site
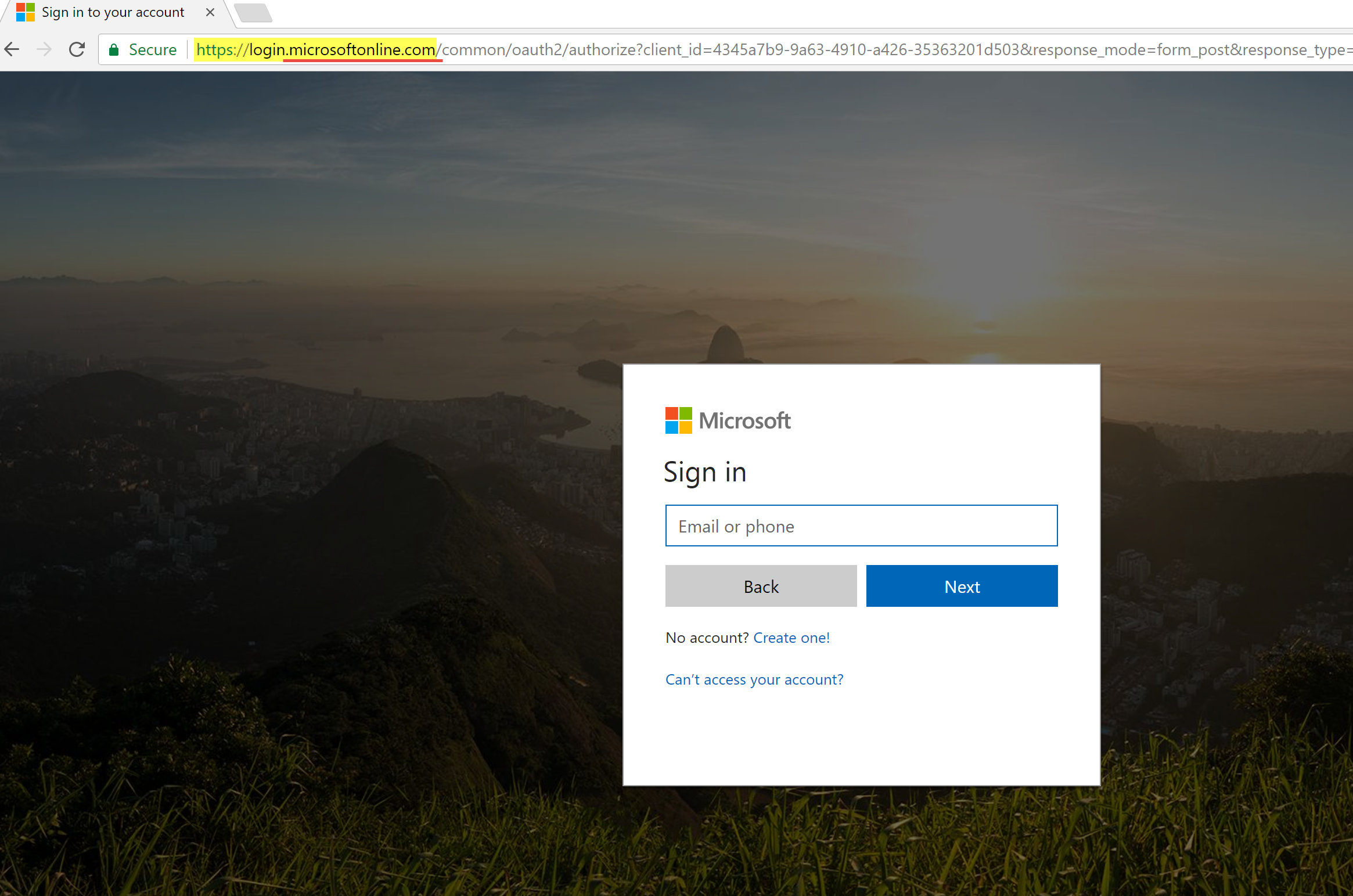
Legitimate Microsoft sites will always have “HTTPS.”
Legitimate sites will have one of the following domains:
- Microsoft.com
- Onmicrosoft.com
- Microsoftonline.com
The Best Defense is Offense
The best protection against phishing scams and social engineering attacks such as these is to be vigilant and proactive. The XPERTECHS Security Operations Center team has adopted several best practices for Microsoft 365 branding that provide immediate visual clues to users – helping them quickly distinguish a legitimate Microsoft 365 login site.
Below are details of a custom Microsoft 365 login experience:
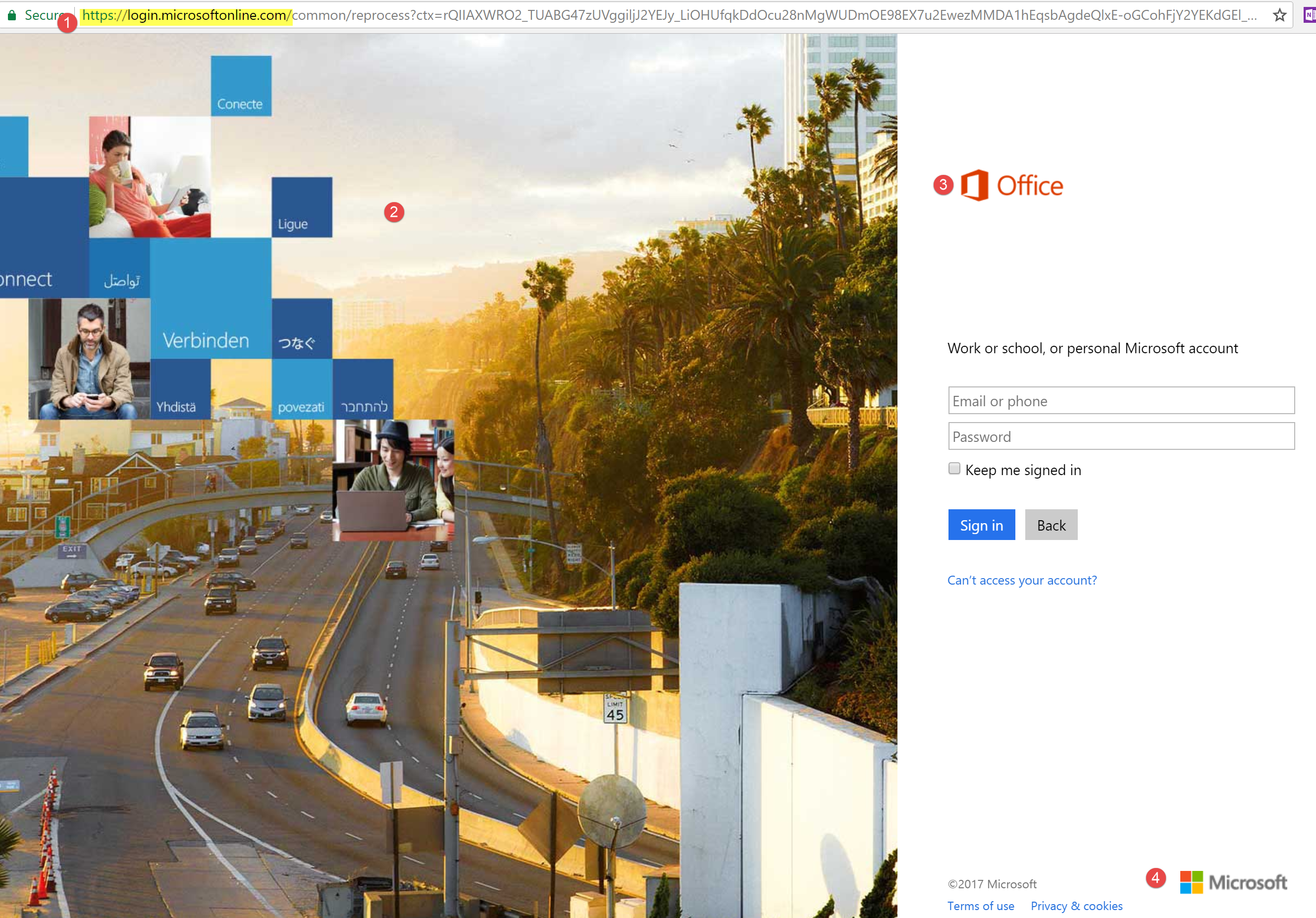
Login to Office365 via the web will always prompt a user with one of two screens:
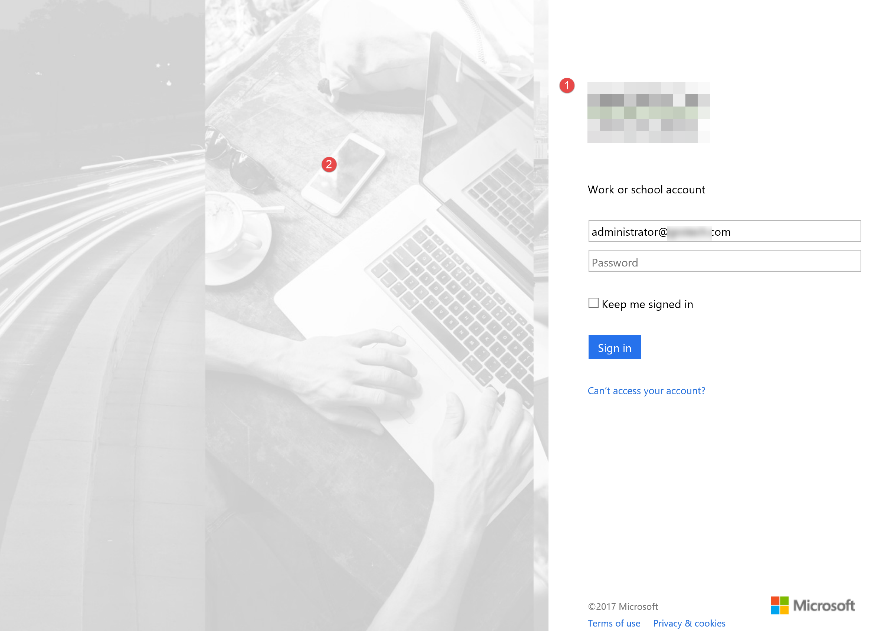
Legacy Office365 Login Page
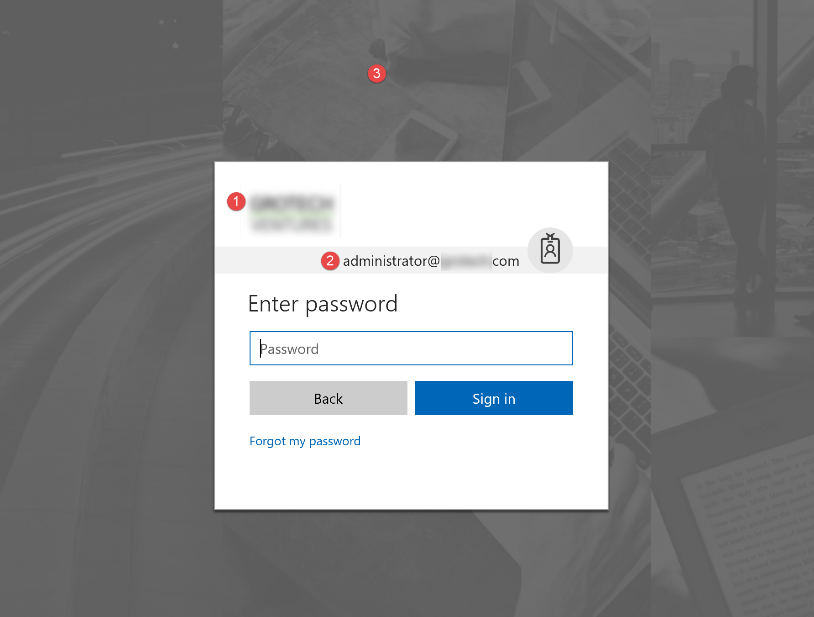
Modern Office365 Login Page
Once the user enters their email address (i.e. user@mydomain.com) the page will immediately refresh with customized graphics and visual logos:
Legacy Office365 Login Page Features:
1. Company Logo
2. Custom Graphic
Modern Office365 Login Page Features:
1. Company Logo
2. Username with Picture (if user has uploaded)
3. Custom Background Logo
Build a Culture of Cybersecurity with XPERTECHS
Keeping your accounts, data and IT systems safe against cyber criminals requires both technical and non-technical tactics. Training your people on how to recognize attempts to steal their Microsoft 365 credentials takes both. Here at XPERTECHS, we’re continually improving cybersecurity in order to keep spam email out of client inboxes. When they do get through, your people need to be savvy about recognizing suspicious messages. That’s where we can help.
XPERTECHS offers industry-leading IT services that cater to the needs of your organization with more know-how, more communication, and more commitment. We are also a certified Gold Partner and Solutions Partner of Microsoft, providing businesses with the knowledge and support they need to fully utilize the capabilities within their Microsoft 365 subscriptions.
Learn more about our Microsoft Modern Workplace Services or schedule a security consultation today to learn how you can up your security game.